Friday, April 16, 2010
How to Remove Newfolder.EXE/Sohanad Virus
You can remove this worm by manual method, or using a removal tool.
1.Manual Method
Here are simple steps following which you can get the worm removed from your system:
1.Download this file:Registry_Repair.
2.Double click on that downloaded registry file, you will be asked weather you’re sure to add this to registry, click yes.
3.Restart your system.
4.Search for the file svhost32.exe and delete it if its found.
5.Search for the file svhost.exe and delete it if its found.
Password Hacking FAQ
1. What are some password basics?
Most accounts on a computer system usually have some method of restricting access to that account, usually in the form of a password. When accessing the system, the user has to present a valid ID to use the system, followed by a password to use the account. Most systems either do not echo the password back on the screen as it is typed, or they print an asterisk in place of the real character.
On most systems,the password is typically ran through some type of algorithm to generate a hash. The hash is usually more than just a scrambled version of the original text that made up the password, it is usually a one-way hash. The one-way hash is a string of characters that cannot be reversed into its original text. You see, most systems do not “decrypt” the stored password during authentication, they store the one-way hash. During the login process, you supply an account and password. The password is ran through an algorithm that generates a one-way hash. This hash is compared to the hash stored on the system. If they are the same, it is assumed the proper password was supplied.
Cryptographically speaking, some algorithms are better than others at generating a one-way hash. The main operating systems we are covering here — NT, Netware, and Unix — all use an algorithm that has been made publically available and has been scrutinized to some degree.
To crack a password requires getting a copy of the one-way hash stored on the server, and then using the algorithm generate your own hash until you get a match. When you get a match, whatever word you used to generate your hash will allow you to log into that system. Since this can be rather time-consuming, automation is typically used. There are freeware password crackers available for NT, Netware, and Unix.
2. Why protect the hashes?
If the one-way hashes are not the password itself but a mathematical derivative, why should they be protected? Well, since the algorithm is already known, a password cracker could be used to simply encrypt the possible passwords and compare the one-way hashes until you get a match. There are two types of approaches to this — dictionary and brute force.
Usually the hashes are stored in a part of the system that has extra security to limit access from potential crackers.
3. What is a dictionary password cracker?
A dictionary password cracker simply takes a list of dictionary words, and one at a time encrypts them to see if they encrypt to the one way hash from the system. If the hashes are equal, the password is considered cracked, and the word tried from the dictionary list is the password.
Some of these dictionary crackers can “manipulate” each word in the wordlist by using filters. These rules/filters allow you to change “idiot” to “1d10t” and other advanced variations to get the most from a word list. The best known of these mutation filters are the rules that come with Crack (for Unix). These filtering rules are so popular they have been ported over to cracking software for NT.
If your dictionary cracker does not have manipulation rules, you can “pre-treat” the wordlist. There are plenty of wordlist manipulation tools that allow all kinds of ways to filter, expand, and alter wordlists. With a little careful planning, you can turn a small collection of wordlists into a very large and thorough list for dictionary crackers without those fancy word manipulations built in.
4. What is a brute force password cracker?
A brute force cracker simply tries all possible passwords until it gets the password. From a cracker perspective, this is usually very time consuming. However, given enough time and CPU power, the password eventually gets cracked.
Most modern brute force crackers allow a number of options to be specified, such as maximum password length or characters to brute force with.
5. Which method is best for cracking?
It really depends on your goal, the cracking software you have, and the operating system you are trying to crack. Let’s go through several scenarios.
If you remotely retrieved the password file through some system bug, your goal may be to simply get logged into that system. With the password file, you now have the user accounts and the hashes. A dictionary attack seems like the quickest method, as you may simply want access to the box. This is typical if you have a method of leveraging basic access to gain god status.
If you already have basic access and used this access to get the password file, maybe you have a particular account you wish to crack. While a couple of swipes with a dictionary cracker might help, brute force may be the way to go.
If your cracking software does both dictionary and brute force, and both are quite slow, you may just wish to kick off a brute force attack and then go about your day. By all means, we recommend a dictionary attack with a pre-treated wordlist first, followed up by brute force only on the accounts you really want the password to.
You should pre-treat your wordlists if the machine you are going to be cracking from bottlenecks more at the CPU than at the disk controller. For example, some slower computers with extremely fast drives make good candidates for large pre-treated wordlists, but if you have the CPU cycles to spare you might want to let the cracking program’s manipulation filters do their thing.
A lot of serious hackers have a large wordlist in both regular and pre-treated form to accommodate either need.
6. What is a salt?
To increase the overhead in cracking passwords, some algorithms employ salts to add further complexity and difficulty to the cracking of passwords. These salts are typically 2 to 8 bytes in length, and algorithmically introduced to further obfuscate the one-way hash. Of the major operating systems covered here, only NT does not use a salt. The specifics for salts for both Unix and Netware systems are covered in their individual password sections.
Historically, the way cracking has been done is to take a potential password, encrypt it and produce the hash, and then compare the result to each account in the password file. By adding a salt, you force the cracker to have to read the salt in and encrypt the potential password with each salt present in the password file. This increases the amount of time to break all of the passwords, although it is certainly no guarantee that the passwords can’t be cracked. Because of this most modern password crackers when dealing with salts do give the option of checking a specific account.
7. What are the dangers of cracking passwords?
The dangers are quite simple, and quite real. If you are caught with a password file you do not have legitimate access to, you are technically in possession of stolen property in the eyes of the law. For this reason, some hackers like to run the cracking on someone else’s systems, thereby limiting their liability. I would only recommend doing this on a system you have a legitimate or well-established account on if you wish to keep a good eye on things, but perhaps have a way of running the cracking software under a different account than your own. This way, if the cracking is discovered (as it often is — cracking is fairly CPU-intensive), it looks to belong to someone else. Obviously, you would want to run this under system adminstrator priviledges as you may have a bit more control, such as assigning lower priority to the cracking software, and hiding the results (making it less obvious to the real administrator).
Being on a system you have legit access to also allows you better access to check on the progress. Of course, if it is known you are a hacker, you’ll still be the first to be blamed whether the cracking software is yours or not!
Running the cracking software in the privacy of your own home has the advantage of allowing you to throw any and all computing power you have at your disposal at a password, but if caught (say you get raided) then there is little doubt whose cracking job is running. However, there are a couple of things you can do to protect yourself: encrypt your files. Only decrypt them when you are viewing them, and wipe and/or encrypt them back after you are done viewing them.
8. Is there any way I can open a password-protected Microsoft Office document?
Certainly! There are plenty of commercial programs that will do this, but we give props to Elcomsoft for fighting the DMCA. 30-day trial versions are available here
Most accounts on a computer system usually have some method of restricting access to that account, usually in the form of a password. When accessing the system, the user has to present a valid ID to use the system, followed by a password to use the account. Most systems either do not echo the password back on the screen as it is typed, or they print an asterisk in place of the real character.
On most systems,the password is typically ran through some type of algorithm to generate a hash. The hash is usually more than just a scrambled version of the original text that made up the password, it is usually a one-way hash. The one-way hash is a string of characters that cannot be reversed into its original text. You see, most systems do not “decrypt” the stored password during authentication, they store the one-way hash. During the login process, you supply an account and password. The password is ran through an algorithm that generates a one-way hash. This hash is compared to the hash stored on the system. If they are the same, it is assumed the proper password was supplied.
Cryptographically speaking, some algorithms are better than others at generating a one-way hash. The main operating systems we are covering here — NT, Netware, and Unix — all use an algorithm that has been made publically available and has been scrutinized to some degree.
To crack a password requires getting a copy of the one-way hash stored on the server, and then using the algorithm generate your own hash until you get a match. When you get a match, whatever word you used to generate your hash will allow you to log into that system. Since this can be rather time-consuming, automation is typically used. There are freeware password crackers available for NT, Netware, and Unix.
2. Why protect the hashes?
If the one-way hashes are not the password itself but a mathematical derivative, why should they be protected? Well, since the algorithm is already known, a password cracker could be used to simply encrypt the possible passwords and compare the one-way hashes until you get a match. There are two types of approaches to this — dictionary and brute force.
Usually the hashes are stored in a part of the system that has extra security to limit access from potential crackers.
3. What is a dictionary password cracker?
A dictionary password cracker simply takes a list of dictionary words, and one at a time encrypts them to see if they encrypt to the one way hash from the system. If the hashes are equal, the password is considered cracked, and the word tried from the dictionary list is the password.
Some of these dictionary crackers can “manipulate” each word in the wordlist by using filters. These rules/filters allow you to change “idiot” to “1d10t” and other advanced variations to get the most from a word list. The best known of these mutation filters are the rules that come with Crack (for Unix). These filtering rules are so popular they have been ported over to cracking software for NT.
If your dictionary cracker does not have manipulation rules, you can “pre-treat” the wordlist. There are plenty of wordlist manipulation tools that allow all kinds of ways to filter, expand, and alter wordlists. With a little careful planning, you can turn a small collection of wordlists into a very large and thorough list for dictionary crackers without those fancy word manipulations built in.
4. What is a brute force password cracker?
A brute force cracker simply tries all possible passwords until it gets the password. From a cracker perspective, this is usually very time consuming. However, given enough time and CPU power, the password eventually gets cracked.
Most modern brute force crackers allow a number of options to be specified, such as maximum password length or characters to brute force with.
5. Which method is best for cracking?
It really depends on your goal, the cracking software you have, and the operating system you are trying to crack. Let’s go through several scenarios.
If you remotely retrieved the password file through some system bug, your goal may be to simply get logged into that system. With the password file, you now have the user accounts and the hashes. A dictionary attack seems like the quickest method, as you may simply want access to the box. This is typical if you have a method of leveraging basic access to gain god status.
If you already have basic access and used this access to get the password file, maybe you have a particular account you wish to crack. While a couple of swipes with a dictionary cracker might help, brute force may be the way to go.
If your cracking software does both dictionary and brute force, and both are quite slow, you may just wish to kick off a brute force attack and then go about your day. By all means, we recommend a dictionary attack with a pre-treated wordlist first, followed up by brute force only on the accounts you really want the password to.
You should pre-treat your wordlists if the machine you are going to be cracking from bottlenecks more at the CPU than at the disk controller. For example, some slower computers with extremely fast drives make good candidates for large pre-treated wordlists, but if you have the CPU cycles to spare you might want to let the cracking program’s manipulation filters do their thing.
A lot of serious hackers have a large wordlist in both regular and pre-treated form to accommodate either need.
6. What is a salt?
To increase the overhead in cracking passwords, some algorithms employ salts to add further complexity and difficulty to the cracking of passwords. These salts are typically 2 to 8 bytes in length, and algorithmically introduced to further obfuscate the one-way hash. Of the major operating systems covered here, only NT does not use a salt. The specifics for salts for both Unix and Netware systems are covered in their individual password sections.
Historically, the way cracking has been done is to take a potential password, encrypt it and produce the hash, and then compare the result to each account in the password file. By adding a salt, you force the cracker to have to read the salt in and encrypt the potential password with each salt present in the password file. This increases the amount of time to break all of the passwords, although it is certainly no guarantee that the passwords can’t be cracked. Because of this most modern password crackers when dealing with salts do give the option of checking a specific account.
7. What are the dangers of cracking passwords?
The dangers are quite simple, and quite real. If you are caught with a password file you do not have legitimate access to, you are technically in possession of stolen property in the eyes of the law. For this reason, some hackers like to run the cracking on someone else’s systems, thereby limiting their liability. I would only recommend doing this on a system you have a legitimate or well-established account on if you wish to keep a good eye on things, but perhaps have a way of running the cracking software under a different account than your own. This way, if the cracking is discovered (as it often is — cracking is fairly CPU-intensive), it looks to belong to someone else. Obviously, you would want to run this under system adminstrator priviledges as you may have a bit more control, such as assigning lower priority to the cracking software, and hiding the results (making it less obvious to the real administrator).
Being on a system you have legit access to also allows you better access to check on the progress. Of course, if it is known you are a hacker, you’ll still be the first to be blamed whether the cracking software is yours or not!
Running the cracking software in the privacy of your own home has the advantage of allowing you to throw any and all computing power you have at your disposal at a password, but if caught (say you get raided) then there is little doubt whose cracking job is running. However, there are a couple of things you can do to protect yourself: encrypt your files. Only decrypt them when you are viewing them, and wipe and/or encrypt them back after you are done viewing them.
8. Is there any way I can open a password-protected Microsoft Office document?
Certainly! There are plenty of commercial programs that will do this, but we give props to Elcomsoft for fighting the DMCA. 30-day trial versions are available here
Hide IP Address – Real ways to hide your IP
Here in this post I will try to give you every possible information to hide the IP address.If you seriously want to hide your IP address then this post is for you!
One of the most frequently asked questions by the internet users is How To Hide IP Address ?. Many times it becomes necessary to hide the real IP address for the sake of privacy.For this, I have tried many softwares, proxy servers and many such tools that guaranteed to hide my IP address.But still none of them worked for me. I think most of you have the same experience.Are you fed up with these dummy softwares that fails to hide the real IP address? Then is there any working way to hide the IP address?
YES, you can definitely hide your IP .
Now I’ll come to the heart of the post, which contains the answer to your curious question How to Hide the IP address ? The only solution to hide your IP address is by using a Proxy Server.But Wait! The story doesn’t end here.Even though proxy servers are the only way to hide your IP address, there are several ways of connecting your PC to the proxy server.Before setting up the connection with the proxy servers you must know some information about different types of proxy servers and their uses.
1. Transparent Proxy Server
This type of proxy server identifies itself as a proxy server and also makes the original IP address available through the http headers. These are generally used to speedup the web browsing since thay have a very good ability to cache websites.But they do not conceal the IP of it’s users. It is widely known as transparent proxy because it will expose your real IP address to the web.This type of proxy server does not hide your IP address.
2. Anonymous Proxy Server
This type of proxy server identifies itself as a proxy server, but does not make the original IP address available. This type of proxy server is detectable, but provides reasonable anonymity for most users. This type of proxy server will hide your IP address.
3. Distorting Proxy Server
This type of proxy server identifies itself as a proxy server, but make an incorrect original IP address available through the http headers. This type of proxy server will hide your IP address.
4. High Anonymity Proxy Server ( Elite Proxy)
This type of proxy server does not identify itself as a proxy server and does not make available the original IP address. This type of proxy server will hide your IP address.So this is the best way to mask your IP.
Which Proxy Server is the best to Hide My IP ?
I know, you can answer this question better than me.Obviously High Anonymity Proxy or Elite Proxy is the best to hide your IP.But it’s not easy to get a list of working elite proxies.If you search the Google, you will definitely get tons of proxy list.You’ll get a list of proxies in the following format
IP:Port Number
Eg: 221.90.45.67:8080 (221.90.45.67 is the IP of the proxy server and 8080 is the port number)
But most of them don’t work.Here are some of the problems/risks associated with using free proxies that are available on the internet.
■Most of them do not work since the proxy servers frequently changes it’s IP/Port number.
■Even if you find a working proxy server it may be too slow.
■Your privacy is not guaranteed since all your traffic is routed through the proxy server.
■The administrators of the proxy servers may steal your valuable information such as passwords,SSN (Social security number),Credit Card details etc.
So with all these being the risks then how to find a Working,fast,Highly Anonymous and secured Proxy servers?
Now I will give a list of softwares that will really hide your IP address.I have tried many such softwares and have found only few of them working perfectly.Here is a list of working IP Hiding softwares that you can try.I have listed them in the order of their popularity
1. Hide The IP
Let’s you choose the country,Type and speed of the proxy.Not so popular but personally I recommend this to the users.
2. Hide My IP
3. Hide IP NG
You can get more informations about these products on their respective homepages.
How to ensure that the IP is hidden ?
Before you hide your IP you can check your real IP by visiting the following site.
WhatIsMyIPAddress.Com
Once you get your real IP, switch on your IP hiding software.Now once again visit the above site and check your IP address.If you see a new IP then this means that your software is doing the right job.Also the above site(Whatismyipaddress.com) is capable of detecting many proxies.If you see the words such as “Suspected proxy server or network sharing device” or similar words then it means that the proxy you are using is not an Elite Proxy.
One Final Word before you leave! Even though Elite proxies are almost undetectable this doesn’t mean that you can escape from online crimes by hiding your IP.There are many proxy detecting services available which detect almost any proxy.So if you involve in any cyber crimes then you will definitely be behind the bars.Using proxy will not help you in this case.
One More thing, It is unsafe to use proxy during e-commerce transactions such as Online banking,Online Credit Card payment etc.So please avoid proxies during these circumstances.
One of the most frequently asked questions by the internet users is How To Hide IP Address ?. Many times it becomes necessary to hide the real IP address for the sake of privacy.For this, I have tried many softwares, proxy servers and many such tools that guaranteed to hide my IP address.But still none of them worked for me. I think most of you have the same experience.Are you fed up with these dummy softwares that fails to hide the real IP address? Then is there any working way to hide the IP address?
YES, you can definitely hide your IP .
Now I’ll come to the heart of the post, which contains the answer to your curious question How to Hide the IP address ? The only solution to hide your IP address is by using a Proxy Server.But Wait! The story doesn’t end here.Even though proxy servers are the only way to hide your IP address, there are several ways of connecting your PC to the proxy server.Before setting up the connection with the proxy servers you must know some information about different types of proxy servers and their uses.
1. Transparent Proxy Server
This type of proxy server identifies itself as a proxy server and also makes the original IP address available through the http headers. These are generally used to speedup the web browsing since thay have a very good ability to cache websites.But they do not conceal the IP of it’s users. It is widely known as transparent proxy because it will expose your real IP address to the web.This type of proxy server does not hide your IP address.
2. Anonymous Proxy Server
This type of proxy server identifies itself as a proxy server, but does not make the original IP address available. This type of proxy server is detectable, but provides reasonable anonymity for most users. This type of proxy server will hide your IP address.
3. Distorting Proxy Server
This type of proxy server identifies itself as a proxy server, but make an incorrect original IP address available through the http headers. This type of proxy server will hide your IP address.
4. High Anonymity Proxy Server ( Elite Proxy)
This type of proxy server does not identify itself as a proxy server and does not make available the original IP address. This type of proxy server will hide your IP address.So this is the best way to mask your IP.
Which Proxy Server is the best to Hide My IP ?
I know, you can answer this question better than me.Obviously High Anonymity Proxy or Elite Proxy is the best to hide your IP.But it’s not easy to get a list of working elite proxies.If you search the Google, you will definitely get tons of proxy list.You’ll get a list of proxies in the following format
IP:Port Number
Eg: 221.90.45.67:8080 (221.90.45.67 is the IP of the proxy server and 8080 is the port number)
But most of them don’t work.Here are some of the problems/risks associated with using free proxies that are available on the internet.
■Most of them do not work since the proxy servers frequently changes it’s IP/Port number.
■Even if you find a working proxy server it may be too slow.
■Your privacy is not guaranteed since all your traffic is routed through the proxy server.
■The administrators of the proxy servers may steal your valuable information such as passwords,SSN (Social security number),Credit Card details etc.
So with all these being the risks then how to find a Working,fast,Highly Anonymous and secured Proxy servers?
Now I will give a list of softwares that will really hide your IP address.I have tried many such softwares and have found only few of them working perfectly.Here is a list of working IP Hiding softwares that you can try.I have listed them in the order of their popularity
1. Hide The IP
Let’s you choose the country,Type and speed of the proxy.Not so popular but personally I recommend this to the users.
2. Hide My IP
3. Hide IP NG
You can get more informations about these products on their respective homepages.
How to ensure that the IP is hidden ?
Before you hide your IP you can check your real IP by visiting the following site.
WhatIsMyIPAddress.Com
Once you get your real IP, switch on your IP hiding software.Now once again visit the above site and check your IP address.If you see a new IP then this means that your software is doing the right job.Also the above site(Whatismyipaddress.com) is capable of detecting many proxies.If you see the words such as “Suspected proxy server or network sharing device” or similar words then it means that the proxy you are using is not an Elite Proxy.
One Final Word before you leave! Even though Elite proxies are almost undetectable this doesn’t mean that you can escape from online crimes by hiding your IP.There are many proxy detecting services available which detect almost any proxy.So if you involve in any cyber crimes then you will definitely be behind the bars.Using proxy will not help you in this case.
One More thing, It is unsafe to use proxy during e-commerce transactions such as Online banking,Online Credit Card payment etc.So please avoid proxies during these circumstances.
10 Tips to Enhance your PC Security
Today almost everyone of us have a PC with an internet connection but how many of us think about it’s security? In fact most of the people are least bothered about their PC’s security.Especially if you have an internet connection safeguarding your PC against network threats is a must.If your PC is not secured then it might be vulnerable to various threats.The threat may be as simple as a virus which corrupts your data or as complex as an identity theft where there are chances of huge loss of money.Did you know that unsecured PCs can be hijacked in minutes ? If you are really concerned about PC security then here are the top 10 security enhancements for your PC.
1. Check Windows Update.Windows Me, 2000, and XP users can configure automatic updates. Click on the Automatic Updates tab in the System control panel and choose the appropriate options.
2. Install a good Antivirus software and update it regularly.An Antivirus without updates is of no use.
3. Install a personal firewall. Both SyGate (http://www.sygate.com//) and ZoneAlarm (http://www.zonelabs.com//) offer free versions.
4. Install a good Antispyware.(Antivirus with built-in antispyware is a go0d choice)
5. Use strong passwords and change them periodically. Passwords should have at least seven characters; use letters and numbers and have at least one symbol. A decent example would be f8izKro#l. This will make it much harder for anyone to gain access to your accounts.
6. If you’re using Outlook or Outlook Express, use the current version or one with the Outlook Security Update installed. The update and current versions patch numerous vulnerabilities.
7. Be skeptical of things on the Internet. Don’t blindly assume that an email “From:” a particular person is actually from that person since it is possible to send a fake email.
8. Check for Versign SSL (Secure Sockets Layer) Certificate (Or logo) before you make any ecommerce transaction (Credit card transaction) with a website.
9. Never disable the Auto-Protect feature of your Antivirus.If your Antivirus doesn’t have Auto-Protect feature then manually scan the files before you execute them.
10. Never give out your passwords to anyone at any time even if the person claims to be from “support.”
1. Check Windows Update.Windows Me, 2000, and XP users can configure automatic updates. Click on the Automatic Updates tab in the System control panel and choose the appropriate options.
2. Install a good Antivirus software and update it regularly.An Antivirus without updates is of no use.
3. Install a personal firewall. Both SyGate (http://www.sygate.com//) and ZoneAlarm (http://www.zonelabs.com//) offer free versions.
4. Install a good Antispyware.(Antivirus with built-in antispyware is a go0d choice)
5. Use strong passwords and change them periodically. Passwords should have at least seven characters; use letters and numbers and have at least one symbol. A decent example would be f8izKro#l. This will make it much harder for anyone to gain access to your accounts.
6. If you’re using Outlook or Outlook Express, use the current version or one with the Outlook Security Update installed. The update and current versions patch numerous vulnerabilities.
7. Be skeptical of things on the Internet. Don’t blindly assume that an email “From:” a particular person is actually from that person since it is possible to send a fake email.
8. Check for Versign SSL (Secure Sockets Layer) Certificate (Or logo) before you make any ecommerce transaction (Credit card transaction) with a website.
9. Never disable the Auto-Protect feature of your Antivirus.If your Antivirus doesn’t have Auto-Protect feature then manually scan the files before you execute them.
10. Never give out your passwords to anyone at any time even if the person claims to be from “support.”
Free Tools for Spyware Removal
There are lot of PC users who know only little about “Spyware”, “Malware”, “hijackers”, “Dialers” & many more. This article will help you avoid pop-ups, spammers and all those baddies.
What is spy-ware?
Spyware is computer software that is installed surreptitiously on a personal computer to intercept or take partial control over the user’s interaction with the computer, without the user’s informed consent.The term spyware suggests software that secretly monitors the user’s behavior.Spyware programs can collect various types of personal information, such as Internet surfing habit, sites that have been visited etc.
How to check if a program has spyware?
It is this little site that keeps a database of programs that are known to install spyware.
Check Out: SpywareGuide
How To Block Pop-Ups?
If you would like to block pop-ups (IE Pop-ups) there are tons of different tools out there, but these are the two best, I think.
Try: Google Toolbar - This tool is a Freeware.
Try: AdMuncher – This tool is a Shareware.
How To Remove Spywares?
If you want to remove spwares then you may try the following tools/programs
Try: Lavasoft Ad-Aware - This tool is a freeware.
Info: Ad-aware is a multi spyware removal utility, that scans your memory, registry and hard drives for known spyware components and lets you remove them. The included backup-manager lets you reinstall a backup, offers and multi language support.
Try: Spybot-S&D – This tool is a freeware.
Info: Detects and removes spyware of different kinds (dialers, loggers, trojans, user tracks) from your computer. Blocks ActiveX downloads, tracking cookies and other threats. Over 10,000 detection files and entries. Provides detailed information about found problems.
Try: Spy Sweeper - This tool is a shareware.
Info: Detects and removes spyware of different kinds (dialers, loggers, trojans, user tracks) from your computer.The best scanner out there, and updated all the time.
Try: BPS Spyware and Adware Remover – This tool is a shareware.
Info: Adware, spyware, trackware and big brotherware removal utility with multi-language support. It scans your memory, registry and drives for known spyware and lets you remove them. Displays a list and lets you select the items you’d like to remove.
How To Prevent Spyware?
To prevent spyware attack you can try the following tools.
Try: SpywareBlaster - This tool is a freeware.
Info: SpywareBlaster doesn’t scan and clean for so-called spyware, but prevents it from being installed in the first place. It achieves this by disabling the CLSIDs of popular spyware ActiveX controls, and also prevents the installation of any of them via a webpage.
Try: XP-AntiSpy - This tool is a freeware.
Info: XP-AntiSpy is a small utility to quickly disable some built-in update and authentication features in WindowsXP that may rise security or privacy concerns in some people
What is spy-ware?
Spyware is computer software that is installed surreptitiously on a personal computer to intercept or take partial control over the user’s interaction with the computer, without the user’s informed consent.The term spyware suggests software that secretly monitors the user’s behavior.Spyware programs can collect various types of personal information, such as Internet surfing habit, sites that have been visited etc.
How to check if a program has spyware?
It is this little site that keeps a database of programs that are known to install spyware.
Check Out: SpywareGuide
How To Block Pop-Ups?
If you would like to block pop-ups (IE Pop-ups) there are tons of different tools out there, but these are the two best, I think.
Try: Google Toolbar - This tool is a Freeware.
Try: AdMuncher – This tool is a Shareware.
How To Remove Spywares?
If you want to remove spwares then you may try the following tools/programs
Try: Lavasoft Ad-Aware - This tool is a freeware.
Info: Ad-aware is a multi spyware removal utility, that scans your memory, registry and hard drives for known spyware components and lets you remove them. The included backup-manager lets you reinstall a backup, offers and multi language support.
Try: Spybot-S&D – This tool is a freeware.
Info: Detects and removes spyware of different kinds (dialers, loggers, trojans, user tracks) from your computer. Blocks ActiveX downloads, tracking cookies and other threats. Over 10,000 detection files and entries. Provides detailed information about found problems.
Try: Spy Sweeper - This tool is a shareware.
Info: Detects and removes spyware of different kinds (dialers, loggers, trojans, user tracks) from your computer.The best scanner out there, and updated all the time.
Try: BPS Spyware and Adware Remover – This tool is a shareware.
Info: Adware, spyware, trackware and big brotherware removal utility with multi-language support. It scans your memory, registry and drives for known spyware and lets you remove them. Displays a list and lets you select the items you’d like to remove.
How To Prevent Spyware?
To prevent spyware attack you can try the following tools.
Try: SpywareBlaster - This tool is a freeware.
Info: SpywareBlaster doesn’t scan and clean for so-called spyware, but prevents it from being installed in the first place. It achieves this by disabling the CLSIDs of popular spyware ActiveX controls, and also prevents the installation of any of them via a webpage.
Try: XP-AntiSpy - This tool is a freeware.
Info: XP-AntiSpy is a small utility to quickly disable some built-in update and authentication features in WindowsXP that may rise security or privacy concerns in some people
Hack Protect your Orkut Account
Most of the people ask me “How to hack an Orkut account” which I have already discussed in my previous post Hacking Orkut. But here I am giving you a detailed information about how to protect your Orkut accounts. As we all know most of the Google services are still in BETA. So,websites like Orkut, powered by Google is not totally secure!Several people feel proud in hacking other user’s account. You do a foolish thing, and next day your account is hacked. This is very sad indeed, but hackers are adding names to their victims list till now.
How can a hacker hack my Orkut account?
The answer to this question is already discussed in my previous post How to Hack Orkut.
But this post is meant for providing some safety measures to prevent your Orkut account from being hacked. There is not much you have to take care of. Just follow the simple steps and never get your orkut account hacked in your life.
1. Never try to login/access your Orkut account from sites other than Orkut.com.
2. Never click on any links from the sources you don’t trust while accessing your Orkut account. (or while accessing any other Google services like Gmail,Blogger etc.)
3. Delete any links on your scrapbook, no matter if a known or unknown person have sent it.
4. Never disclose your orkut login details with anyone.
5. Never ever use Javascripts on Orkut, no matter whatever it claims to do. Get satisfied with the services provided by default! Avoid using third party Scripts which might be malicious.
6. Never get excited to see a site claiming to have 1000 cool orkut tricks for which you have to just log in to your orkut account. Don’t trust that site. That’s a Phishing site.
7. Never tick the box “REMEMBER ME” on the orkut homepage if you are surfing from a cafe or a public area.
8. Always remember to hit Sign out button, when you are done.
Know More About Trojans and Backdoors
A Trojan horse is an unauthorized program contained within a legitimate program. This unauthorized program performs functions unknown (and probably unwanted) by the user.
■It is a legitimate program that has been altered by the placement of unauthorized code within it; this code performs functions unknown (and probably unwanted) by the user.
■Any program that appears to perform a desirable and necessary function but that (because of unauthorized code within it that is unknown to the user) performs functions unknown (and definitely unwanted) by the user.
Working of Trojans
■Attacker gets access to the trojaned system as the system goes online
■By way of the access provided by the trojan attacker can stage attacks of different types.
Various Trojan Types
■Remote Access Trojans
■Password Sending Trojans
■Keyloggers
■Destructive
■Denial Of Service (DoS) Attack Trojans
■Proxy/Wingate Trojans
■FTP Trojans
■Software Detection Killers
Modes of Transmission
■Attachments
■Physical Access
■Browser And E-mail Software Bugs
■NetBIOS (File Sharing)
■Fake Programs
■Un-trusted Sites And Freeware Software
Backdoor Countermeasures
■Most commercial ant-virus products can automatically scan and detect backdoor programs before they can cause damage (Eg. before accessing a floppy, running exe or downloading mail)
■An inexpensive tool called Cleaner (http://www.moosoft.com/cleanet.html) can identify and eradicate 1000 types of backdoor programs and trojans.
■Educate your users not to install applications downloaded from the internet and e-mail attachments.
■It is a legitimate program that has been altered by the placement of unauthorized code within it; this code performs functions unknown (and probably unwanted) by the user.
■Any program that appears to perform a desirable and necessary function but that (because of unauthorized code within it that is unknown to the user) performs functions unknown (and definitely unwanted) by the user.
Working of Trojans
■Attacker gets access to the trojaned system as the system goes online
■By way of the access provided by the trojan attacker can stage attacks of different types.
Various Trojan Types
■Remote Access Trojans
■Password Sending Trojans
■Keyloggers
■Destructive
■Denial Of Service (DoS) Attack Trojans
■Proxy/Wingate Trojans
■FTP Trojans
■Software Detection Killers
Modes of Transmission
■Attachments
■Physical Access
■Browser And E-mail Software Bugs
■NetBIOS (File Sharing)
■Fake Programs
■Un-trusted Sites And Freeware Software
Backdoor Countermeasures
■Most commercial ant-virus products can automatically scan and detect backdoor programs before they can cause damage (Eg. before accessing a floppy, running exe or downloading mail)
■An inexpensive tool called Cleaner (http://www.moosoft.com/cleanet.html) can identify and eradicate 1000 types of backdoor programs and trojans.
■Educate your users not to install applications downloaded from the internet and e-mail attachments.
How to create a self-signed SSL Certificate ...
Overview
The following is an extremely simplified view of how SSL is implemented and what part the certificate plays in the entire process.
Normal web traffic is sent unencrypted over the Internet. That is, anyone with access to the right tools can snoop all of that traffic. Obviously, this can lead to problems, especially where security and privacy is necessary, such as in credit card data and bank transactions. The Secure Socket Layer is used to encrypt the data stream between the web server and the web client (the browser).
SSL makes use of what is known as asymmetric cryptography, commonly referred to as public key cryptography (PKI). With public key cryptography, two keys are created, one public, one private. Anything encrypted with either key can only be decrypted with its corresponding key. Thus if a message or data stream were encrypted with the server's private key, it can be decrypted only using its corresponding public key, ensuring that the data only could have come from the server.
If SSL utilizes public key cryptography to encrypt the data stream traveling over the Internet, why is a certificate necessary? The technical answer to that question is that a certificate is not really necessary - the data is secure and cannot easily be decrypted by a third party. However, certificates do serve a crucial role in the communication process. The certificate, signed by a trusted Certificate Authority (CA), ensures that the certificate holder is really who he claims to be. Without a trusted signed certificate, your data may be encrypted, however, the party you are communicating with may not be whom you think. Without certificates, impersonation attacks would be much more common.
Step 1: Generate a Private Key
The openssl toolkit is used to generate an RSA Private Key and CSR (Certificate Signing Request). It can also be used to generate self-signed certificates which can be used for testing purposes or internal usage.
The first step is to create your RSA Private Key. This key is a 1024 bit RSA key which is encrypted using Triple-DES and stored in a PEM format so that it is readable as ASCII text.
openssl genrsa -des3 -out server.key 1024
Generating RSA private key, 1024 bit long modulus
.........................................................++++++
........++++++
e is 65537 (0x10001)
Enter PEM pass phrase:
Verifying password - Enter PEM pass phrase:
Step 2: Generate a CSR (Certificate Signing Request)
Once the private key is generated a Certificate Signing Request can be generated. The CSR is then used in one of two ways. Ideally, the CSR will be sent to a Certificate Authority, such as Thawte or Verisign who will verify the identity of the requestor and issue a signed certificate. The second option is to self-sign the CSR, which will be demonstrated in the next section.
During the generation of the CSR, you will be prompted for several pieces of information. These are the X.509 attributes of the certificate. One of the prompts will be for "Common Name (e.g., YOUR name)". It is important that this field be filled in with the fully qualified domain name of the server to be protected by SSL. If the website to be protected will be https://public.akadia.com, then enter public.akadia.com at this prompt. The command to generate the CSR is as follows:
openssl req -new -key server.key -out server.csr
Country Name (2 letter code) [GB]:CH
State or Province Name (full name) [Berkshire]:Bern
Locality Name (eg, city) [Newbury]:Oberdiessbach
Organization Name (eg, company) [My Company Ltd]:Akadia AG
Organizational Unit Name (eg, section) []:Information Technology
Common Name (eg, your name or your server's hostname) []:public.akadia.com
Email Address []:martin dot zahn at akadia dot ch
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
Step 3: Remove Passphrase from Key
One unfortunate side-effect of the pass-phrased private key is that Apache will ask for the pass-phrase each time the web server is started. Obviously this is not necessarily convenient as someone will not always be around to type in the pass-phrase, such as after a reboot or crash. mod_ssl includes the ability to use an external program in place of the built-in pass-phrase dialog, however, this is not necessarily the most secure option either. It is possible to remove the Triple-DES encryption from the key, thereby no longer needing to type in a pass-phrase. If the private key is no longer encrypted, it is critical that this file only be readable by the root user! If your system is ever compromised and a third party obtains your unencrypted private key, the corresponding certificate will need to be revoked. With that being said, use the following command to remove the pass-phrase from the key:
cp server.key server.key.org
openssl rsa -in server.key.org -out server.key
The newly created server.key file has no more passphrase in it.
-rw-r--r-- 1 root root 745 Jun 29 12:19 server.csr
-rw-r--r-- 1 root root 891 Jun 29 13:22 server.key
-rw-r--r-- 1 root root 963 Jun 29 13:22 server.key.org
Step 4: Generating a Self-Signed Certificate
At this point you will need to generate a self-signed certificate because you either don't plan on having your certificate signed by a CA, or you wish to test your new SSL implementation while the CA is signing your certificate. This temporary certificate will generate an error in the client browser to the effect that the signing certificate authority is unknown and not trusted.
To generate a temporary certificate which is good for 365 days, issue the following command:
openssl x509 -req -days 365 -in server.csr -signkey server.key -out server.crt
Signature ok
subject=/C=CH/ST=Bern/L=Oberdiessbach/O=Akadia AG/OU=Information
Technology/CN=public.akadia.com/Email=martin dot zahn at akadia dot ch
Getting Private key
Step 5: Installing the Private Key and Certificate
When Apache with mod_ssl is installed, it creates several directories in the Apache config directory. The location of this directory will differ depending on how Apache was compiled.
cp server.crt /usr/local/apache/conf/ssl.crt
cp server.key /usr/local/apache/conf/ssl.key
Step 6: Configuring SSL Enabled Virtual Hosts
SSLEngine on
SSLCertificateFile /usr/local/apache/conf/ssl.crt/server.crt
SSLCertificateKeyFile /usr/local/apache/conf/ssl.key/server.key
SetEnvIf User-Agent ".*MSIE.*" nokeepalive ssl-unclean-shutdown
CustomLog logs/ssl_request_log \
"%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"
Step 7: Restart Apache and Test
/etc/init.d/httpd stop
/etc/init.d/httpd stop
https://public.akadia.com
source
http://akadia.com
Know More About Secure Sockets Layer (SSL)
Secure Sockets Layer (SSL) is the most widely used technology for providing a secure communication between the web client and the web server. Most of us are familiar with many sites such as Gmail, Yahoo etc. using https protocol in their login pages. When we see this, we may wonder what’s the difference between http and https. In simple words HTTP protocol is used for standard communication between the Web server and the client. HTTPS is used for a SECURE communication.
What exactly is Secure Communication ?
Suppose there exists two communication parties A (client) and B (server).
Working of HTTP
When A sends a message to B, the message is sent as a plain text in an unencrypted manner. This is acceptable in normal situations where the messages exchanged are not confidential. But imagine a situation where A sends a PASSWORD to B. In this case, the password is also sent as a plain text. This has a serious security problem because, if an intruder (hacker) can gain unauthorised access to the ongoing communication between A and B , he can see the PASSWORDS since they remain unencrypted. This scenario is illustrated using the following figure
Now lets see the working of HTTPS
When A sends a PASSWORD (say “mypass“) to B, the message is sent in an encrypted format. The encrypted message is decrypted on B’s side. So even if the Hacker gains an unauthorised access to the ongoing communication between A and B he gets only the encrypted password (“xz54p6kd“) and not the original password. This is shown below
How is HTTPS implemented ?
HTTPS is implemented using Secure Sockets Layer (SSL).A website can implement HTTPS by purchasing an SSL Certificate. Secure Sockets Layer (SSL) technology protects a Web site and makes it easy for the Web site visitors to trust it. It has the following uses
1.An SSL Certificate enables encryption of sensitive information during online transactions.
2.Each SSL Certificate contains unique, authenticated information about the certificate owner.
3.A Certificate Authority verifies the identity of the certificate owner when it is issued.
How Encryption Works ?
Each SSL Certificate consists of a Public key and a Private key. The public key is used to encrypt the information and the private key is used to decrypt it. When your browser connects to a secure domain, the server sends a Public key to the browser to perform the encryption. The public key is made available to every one but the private key(used for decryption) is kept secret. So during a secure communication, the browser encrypts the message using the public key and sends it to the server. The message is decrypted on the server side using the Private key(Secret key).
How to identify a Secure Connection ?
In Internet Explorer, you will see a lock icon in the Security Status bar. The Security Status bar is located on the right side of the Address bar.You can click the lock to view the identity of the website.
In high-security browsers, the authenticated organization name is prominently displayed and the address bar turns GREEN when an Extended Validation SSL Certificate is detected. If the information does not match or the certificate has expired, the browser displays an error message or warning and the status bar may turn RED.
So the bottom line is, whenever you perform an online transaction such as Credit card payment, Bank login or Email login always ensure that you have a secure communication. A secure communication is a must in these situations.Otherwise there are chances of Phishing using a Fake login Page.
I Hope this helps.Please pass your comments.
12 Tips to Maintain a Virus Free Computer
Is your computer infected with virus? Do you often get mysterious error messages? Well this is a common problem faced by almost all the computer users across the globe. There are many viruses and worms out there that could infect your computer. Some are harmless, but, they do have the capacity to do any number of nasty things, up to and including, erasing all data from your computer. However there are ways to keep viruses away from your PC. Here are the 12 tips to maintain a virus free computer.
1. Email is one of the common ways by which your computer can catch a virus. So it is always recommended to stay away from SPAM. Open only those emails that has it’s origin from a trusted source such as those which comes from your contact list. If you are using your own private email host (other than gmail, yahoo, hotmail etc.) then it is highly recommended that you use a good anti-spam software. And finally NEVER click on any links in the emails that comes from untrusted sources.
2. USB thumb/pen drives is another common way by which viruses spread rapidly. So it is always a good habit to perform a virus scan before copying any data onto your computer. NEVER double-click the pen drive to open it. Instead right-click on it and select the option “open”. This is a safe way to open a pen drive.
3. Be careful about using MS Outlook. Outlook is more susceptible to worms than other e-mail programs, unless you have efficient Anti-Virus programs running. Use Pegasus or Thunderbird (by Mozilla), or a web-based program such as Hotmail or Yahoo (In Firefox).
4. As we all know, Internet is the main source of all the malicious programs including viruses, worms, trojans etc. In fact Internet contributes to virus infection by up to 80%. So here are the tips for safe surfing habits so that you can ward off virus infection up to the maximum extent.
■Don’t click on pop-up windows that announce a sudden disaster in your city or announce that you’ve won an hourly prize. They are the ways to mislead Internet users and you should never trust them.
■You can also use a pop-up blocker to automatically block those pop-ups.
5. Most of us use search engines like Google to find what we are looking for. It is quite obvious for a malicious website to get listed in the search results. So to avoid visiting those untrusted malicious websites, you can download and install the AVG LinkScanner which is a freeware. This tool can become very handy and will help you to stay away from malicious websites.
6. Install a good antivirus software and keep it updated. Also perform full system scan periodically. It is highly recommended that you turn on the automatic update feature. This is the most essential task to protect your PC from virues. If PC security is your first option then it is recommended that you go for a shareware antivirus software over the free ones. Most of the antivirus supports the Auto-Protect feature that provides realtime security for your PC. Make sure that this feature is turned on.
7. Install a good Antispyware program, that operates against Internet malware and spyware.
8. Never open any email attachments that come from untrusted sources. If it is a picture, text or sound file (these attachments end in the extensions .txt, .jpeg, .gif, .bmp, .tif, .mp3, .htm, .html, and .avi), you are probably safe, but still do a scan before opening.
9. Do not use disks that other people gave you, even from work. The disk could be infected with a virus. Of course, you can run a virus scan on it first to check it out.
10. Set up your Windows Update to automatically download patches and upgrades. This will allow your computer to automatically download any updates to both the operating system and Internet Explorer. These updates fix security holes in both pieces of software.
11. While you download files from untrusted websites/sources such as torrents, warez etc. make sure that you run a virus scan before executing them.
12. And finally it is recommended not to visit the websites that feature illegal/unwanted stuffs such as cracks, serials, warez etc. since they contribute much in spreading of viruses and other malicious programs
1. Email is one of the common ways by which your computer can catch a virus. So it is always recommended to stay away from SPAM. Open only those emails that has it’s origin from a trusted source such as those which comes from your contact list. If you are using your own private email host (other than gmail, yahoo, hotmail etc.) then it is highly recommended that you use a good anti-spam software. And finally NEVER click on any links in the emails that comes from untrusted sources.
2. USB thumb/pen drives is another common way by which viruses spread rapidly. So it is always a good habit to perform a virus scan before copying any data onto your computer. NEVER double-click the pen drive to open it. Instead right-click on it and select the option “open”. This is a safe way to open a pen drive.
3. Be careful about using MS Outlook. Outlook is more susceptible to worms than other e-mail programs, unless you have efficient Anti-Virus programs running. Use Pegasus or Thunderbird (by Mozilla), or a web-based program such as Hotmail or Yahoo (In Firefox).
4. As we all know, Internet is the main source of all the malicious programs including viruses, worms, trojans etc. In fact Internet contributes to virus infection by up to 80%. So here are the tips for safe surfing habits so that you can ward off virus infection up to the maximum extent.
■Don’t click on pop-up windows that announce a sudden disaster in your city or announce that you’ve won an hourly prize. They are the ways to mislead Internet users and you should never trust them.
■You can also use a pop-up blocker to automatically block those pop-ups.
5. Most of us use search engines like Google to find what we are looking for. It is quite obvious for a malicious website to get listed in the search results. So to avoid visiting those untrusted malicious websites, you can download and install the AVG LinkScanner which is a freeware. This tool can become very handy and will help you to stay away from malicious websites.
6. Install a good antivirus software and keep it updated. Also perform full system scan periodically. It is highly recommended that you turn on the automatic update feature. This is the most essential task to protect your PC from virues. If PC security is your first option then it is recommended that you go for a shareware antivirus software over the free ones. Most of the antivirus supports the Auto-Protect feature that provides realtime security for your PC. Make sure that this feature is turned on.
7. Install a good Antispyware program, that operates against Internet malware and spyware.
8. Never open any email attachments that come from untrusted sources. If it is a picture, text or sound file (these attachments end in the extensions .txt, .jpeg, .gif, .bmp, .tif, .mp3, .htm, .html, and .avi), you are probably safe, but still do a scan before opening.
9. Do not use disks that other people gave you, even from work. The disk could be infected with a virus. Of course, you can run a virus scan on it first to check it out.
10. Set up your Windows Update to automatically download patches and upgrades. This will allow your computer to automatically download any updates to both the operating system and Internet Explorer. These updates fix security holes in both pieces of software.
11. While you download files from untrusted websites/sources such as torrents, warez etc. make sure that you run a virus scan before executing them.
12. And finally it is recommended not to visit the websites that feature illegal/unwanted stuffs such as cracks, serials, warez etc. since they contribute much in spreading of viruses and other malicious programs
Registry Repair Tips
This article explains how to inspect and repair registry errors to improve the performance of your PC. If you are a Windows user then you will most probably be aware of the fact that the registry gets corrupted over time resulting in an overall decreased performance of your computer. At times registry errors can also make your PC to freeze down and hang up every now and then causing a serious annoyance to the user. At this point, the registry needs a serious repair to bring your PC back to it’s life. Well before I tell you how to repair the registry lets see what causes registry to get corrupted.
Registry errors may occur due to installing too many applications/softwares from time to time without verifying the publishers. This may create invalid entries in the registry hive leading to errors. With the Internet boom and the era of freeware with free downloads, people often install programs from untrusted sources which results in serious damage to the registry. Since the registry is a crucial component of the Windows operating system, damage to this registry can cause system performance to drop down considerably.
How to Repair the Registry?
The best and the easiest way to repair your registry is by using a Registry Repair Tool (Registry Cleaner) which will automatically scan the registry to find invalid entries and will repair it by removing the errors with in no time. A registry cleaner is the simple and safest solution to repair registry and bring your PC back to it’s life without the need to re-install the Windows. We recommend the following registry cleaner to repair the Windows registry
Perfect Optimizer
Perfect Optimizer is one of the best and award winning registry cleaner that repairs registry to avoid PC errors such as unwanted shutdown, freezing, crashing and more. Perfect optimizer will
■Repair registry and increases your PC performance by upto 70%
■Repair registry to fix DLL errors and invalid shortcuts
■Free up virtual memory to avoid error messages
■Performs Defragmentation and Compression of the registry
■Repair registry to fix blue screen errors, system crashes, startup errors and more…
Visit Perfect Optimizer Homepage for more information on this program.
Can I Manually Repair the Registry?
Windows registry has a very complex structure with hundreds of thousands of entries embedded in it. A corrupt registry may contain thousands of invalid entries and errors in it and hence it is impractical and almost impossible to manually inspect, find and repair those errors. Also manual registry repair involves serious risk and can lead to a total system break down if done improperly. Except you are a highly experienced Windows user or a Windows expert, users are not encouraged to tamper with the registry.
Hence using a registry repair tool is the safest and easiest way to repair the registry and improve the overall performance of your PC. Registry repair tools will not only repair the registry but also maintains it’s health in a good condition so as to avoid any future damage to it. It is recommended that you periodically (daily or weekly) perform registry scans using these tools to repair the errors as and when they come up and keep your PC’s health at it’s best. Repair the registry and make your PC blazing fast like never before!
Registry errors may occur due to installing too many applications/softwares from time to time without verifying the publishers. This may create invalid entries in the registry hive leading to errors. With the Internet boom and the era of freeware with free downloads, people often install programs from untrusted sources which results in serious damage to the registry. Since the registry is a crucial component of the Windows operating system, damage to this registry can cause system performance to drop down considerably.
How to Repair the Registry?
The best and the easiest way to repair your registry is by using a Registry Repair Tool (Registry Cleaner) which will automatically scan the registry to find invalid entries and will repair it by removing the errors with in no time. A registry cleaner is the simple and safest solution to repair registry and bring your PC back to it’s life without the need to re-install the Windows. We recommend the following registry cleaner to repair the Windows registry
Perfect Optimizer
Perfect Optimizer is one of the best and award winning registry cleaner that repairs registry to avoid PC errors such as unwanted shutdown, freezing, crashing and more. Perfect optimizer will
■Repair registry and increases your PC performance by upto 70%
■Repair registry to fix DLL errors and invalid shortcuts
■Free up virtual memory to avoid error messages
■Performs Defragmentation and Compression of the registry
■Repair registry to fix blue screen errors, system crashes, startup errors and more…
Visit Perfect Optimizer Homepage for more information on this program.
Can I Manually Repair the Registry?
Windows registry has a very complex structure with hundreds of thousands of entries embedded in it. A corrupt registry may contain thousands of invalid entries and errors in it and hence it is impractical and almost impossible to manually inspect, find and repair those errors. Also manual registry repair involves serious risk and can lead to a total system break down if done improperly. Except you are a highly experienced Windows user or a Windows expert, users are not encouraged to tamper with the registry.
Hence using a registry repair tool is the safest and easiest way to repair the registry and improve the overall performance of your PC. Registry repair tools will not only repair the registry but also maintains it’s health in a good condition so as to avoid any future damage to it. It is recommended that you periodically (daily or weekly) perform registry scans using these tools to repair the errors as and when they come up and keep your PC’s health at it’s best. Repair the registry and make your PC blazing fast like never before!
Change the Title of Yahoo Messenger
Here’s how you change the title text that appears at the top of the Messenger window. By default, this is “Yahoo! Messenger”, followed by your status. Simply edit the ymsgr.ini file, which you will find in the same folder as the Messenger program, in your Program Files folder. Locate the file and open it in Notepad. Then, at the end, add the following:
[APP TITLE]
caption=YOUR TEXT
Here, “YOUR TEXT” is whatever you want in the title bar. Save the file and close Messenger. When you restart it you will see your text in the title bar.
[APP TITLE]
caption=YOUR TEXT
Here, “YOUR TEXT” is whatever you want in the title bar. Save the file and close Messenger. When you restart it you will see your text in the title bar.
Hacking Yahoo Messenger
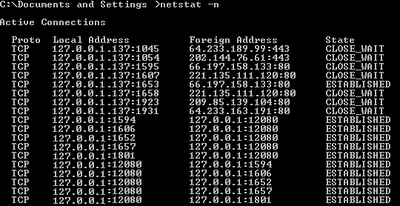
This tutorial will tell you how to hack yahoo messenger while you are engaged in chatting with some person.While you are chatting through yahoo messenger, Yahoo will hide the IP addresses of all the computers that are connected through the yahoo messenger application to the chat room.So it is not possible to directly find out the IP of the person you want to hack.Then how to get the IP address? Yes it is still possible to hack the IP address during the Yahoo messenger chat.The procedure to Hack Yahoo messenger is discussed in detail below.
While you are chatting via yahoo messenger the communication between you and the person you want to hack, takes place indirectly via Yahoo server and not directly.It is not possible to hack Yahoo messenger directly to get the IP address.So to hack his IP, you must establish a direct communication with him.So,how to do this? It’s easy.Just start chatting with some one via Yahoo messenger.During the process of chatting send him a big file.Now the file transfer takes place directly between your computer and the victim’s computer(via yahoo messenger application).So now, you are ready to go. Here’s the step-by-step process to hack Yahoo messenger and get the IP address of the person .
■Goto the COMMAND PROMPT (START>>>RUN>>>Type CMD).
■Here Type “netstat -n” (without quotes).
NOTE: If you are new to “netstat” and other IP related commands refer this tutorial:Windows XP IP Utilities
■The pic given below shows netstat results of my computer.I was not chatting when i took this pic and hence it looks modified.
■Here local address is your own IP and the foreign address is the IP address of the recipient with whom you are connected via yahoo messenger (There may be multiple recipients and hence multiple foreign addresses).
■Now send him the file.
■Check the output by typing the command “netstat -n” (without quotes).
■Assume the output is something like this.
TCP 127.0.0.10:5101 124.55.23.11:1246 ESTABLISHED
Here 124.55.23.11 is the IP address of the person with whom you are chatting and 1246 is the port number where connection is established.That’s It! You have now hacked Yahoo messenger to get his IP address.
Once you hack Yahoo messenger and get his IP address you can use any of the Remote Administration tools or perform NETBIOS HACKING.Refer this tutorial on Netbios Hacking.
NOTE: Some times there are chances where in the file transfer gets encrypted (takes place via yahoo server itself).So in this case the above hack may fail to work.
While you are chatting via yahoo messenger the communication between you and the person you want to hack, takes place indirectly via Yahoo server and not directly.It is not possible to hack Yahoo messenger directly to get the IP address.So to hack his IP, you must establish a direct communication with him.So,how to do this? It’s easy.Just start chatting with some one via Yahoo messenger.During the process of chatting send him a big file.Now the file transfer takes place directly between your computer and the victim’s computer(via yahoo messenger application).So now, you are ready to go. Here’s the step-by-step process to hack Yahoo messenger and get the IP address of the person .
■Goto the COMMAND PROMPT (START>>>RUN>>>Type CMD).
■Here Type “netstat -n” (without quotes).
NOTE: If you are new to “netstat” and other IP related commands refer this tutorial:Windows XP IP Utilities
■The pic given below shows netstat results of my computer.I was not chatting when i took this pic and hence it looks modified.
■Here local address is your own IP and the foreign address is the IP address of the recipient with whom you are connected via yahoo messenger (There may be multiple recipients and hence multiple foreign addresses).
■Now send him the file.
■Check the output by typing the command “netstat -n” (without quotes).
■Assume the output is something like this.
TCP 127.0.0.10:5101 124.55.23.11:1246 ESTABLISHED
Here 124.55.23.11 is the IP address of the person with whom you are chatting and 1246 is the port number where connection is established.That’s It! You have now hacked Yahoo messenger to get his IP address.
Once you hack Yahoo messenger and get his IP address you can use any of the Remote Administration tools or perform NETBIOS HACKING.Refer this tutorial on Netbios Hacking.
NOTE: Some times there are chances where in the file transfer gets encrypted (takes place via yahoo server itself).So in this case the above hack may fail to work.